Web worm crashes computers around globe
Thousands of PCs across city among those affected by 'LovSan' virus that attacks Windows operating systems
A worm virus snaked its way around computer networks Tuesday, shutting down tens of thousands of computers worldwide, including hundreds — if not thousands — in Lawrence.
The virus exploits a security hole in Microsoft Corp.’s Windows operating systems that was announced last month. Despite the warning and a free patch that was available, many people and businesses were vulnerable — and infected.
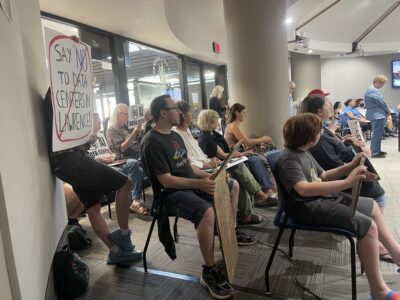
“I never heard anything about this patch,” said John Hamm, a volunteer working to repair a crashed computer at Kansas Advocates for Better Care in Lawrence. “If everyone else is having the problems I’m having, we’re all in trouble.”
The infection was dubbed “blaster” and “LovSan,” because of a love note left behind on vulnerable computers: “I just want to say LOVE YOU SAN!”
Researchers discovered another message hidden inside the infection that appeared to taunt Microsoft Chairman Bill Gates: “billy gates why do you make this possible? Stop making money and fix your software!”
Government and industry experts have anticipated such an outbreak since July 16, when Microsoft acknowledged the flaw affected nearly all versions of its flagship Windows operating system software.
No attachments
The virus spreads over the Internet on its own, burrowing into a computer through the Windows flaw without need for user intervention. Most viruses are the result of the computer user opening an attached file on an e-mail.
“Even if you make sure not to click on anything, you’re not protected. It arrives on your computer through regular network traffic. There’s nothing you can do about it,” said Joe Hartman, director of North American Research for Trend Micro, a provider of anti-virus software.
As on most machines with the virus, Hamm said the computer he was working on began shutting down and restarting on its own. He said he removed the virus and attempted to download the patch from the Microsoft Web site, only to have the virus re-appear on the computer’s system.
“We’re having all sorts of trouble,” he said mid-afternoon, after working on it for several hours. “We still haven’t got it cleared.”
By 4:30 p.m., he had the system back online.
Worldwide snarl
The worm was reported Monday in the United States and was snarling networks Tuesday, wreaking havoc on systems around the globe. In Sweden, Internet provider Telia Sonera said about 20,000 of its customers were affected after the infection clogged 40 servers that handled Internet traffic. Automaker BMW in Germany reported problems, as did some Danish companies.
In Lawrence, Sunflower Broadband customers were among the hardest hit.
| What to do if your computer has been infected by the “LovSan” worm:¢ Go to www.microsoft.com for the appropriate patch.¢ Trend Micro’s free anti-virus scanner, HouseCall, (www.trendmicro.com) will determine if your system has been infected and download the patch. Joe Hartman, director of North American Research for Trend Micro, said no information was collected from computers using the HouseCall scanner.¢ Central Command’s site, www.centralcommand.com, also has details on how to detect and fix the problem. |
Frank Wiles, a Sunflower system administrator, said the company had disabled cable modem service to 300 infected customers by mid-afternoon Monday in an attempt to stop the spread. He expected an additional 700 users to be disabled by the end of the week. The company has about 12,000 cable modem users.
Sunflower Broadband is owned by The World Company, which also owns the Journal-World.
Wiles said that despite Microsoft’s warnings, most users didn’t take precautions against the virus.
“Most people didn’t patch,” he said. “In less than 24 hours it’s become the most prevalent virus there is.”
‘Like wildfire’
Scott Hasty, owner of UNI Computers of Kansas, 1403 W. 23rd St., said he started receiving phone calls about the virus Monday. He had received about 20 more by mid-afternoon Tuesday.
“It spread like wildfire,” he said. “This is going to affect home users big-time.”
He said the only way to remedy the problem was to remove the virus and download the patch from the Microsoft Web site. The challenge, he said, is downloading the patch when you’ve been kicked off the Internet or your computer won’t stay on long enough to complete the download.
“Get the patch installed now,” he advised. “The virus will continue to linger out there.”
Once a computer is infected, the worm also installs instructions for a midnight Aug. 16 attack on Microsoft’s Windows Update Web site — the same site that users are encouraged to go to for downloading patches that would protect their systems from this worm and others. The worm then scans the Internet for other vulnerable computers.
Though some home users were caught unprepared, larger institutions in Lawrence said they had taken proper safety precautions.
State government computer systems were not harmed, according to Caleb Asher, a spokesman for the Kansas Department of Administration.
“It appears everything is OK,” he said, attributing the success of the system to maintaining up-to-date anti-virus software.
At Lawrence, KU
City of Lawrence computers have a routine software updating system that downloads updates for virus protection.
“That already downloaded the specific protection for the worm,” said Lisa Patterson, a city spokeswoman. “The software was pretty well prepared for it.”
At Kansas University, computer technicians worked for three weeks to install the Microsoft patch on more than 1,000 computers. Allison Rose Lopez, external relations director for information services, said a handful of KU users without the patch were infected with the virus, but she didn’t have exact figures.
“The campus network is being very well maintained,” she said. “We knew this was coming. Our phones aren’t ringing off the hook.”
Security experts said the world was lucky this time because LovSan is comparatively mild and doesn’t destroy files. They worry that a subsequent attack exploiting the same flaw — one of the most severe to afflict Windows — could be much more damaging.
“We think we’re going to be dealing with it for quite some time,” said Dan Ingevaldson, engineering manager at Internet Security Systems in Atlanta.
Tracing the worm’s origins will be difficult because it left few clues, said Marc Maiffret, co-founder of eEye Digital Security. The worm appeared based on code released earlier by a Chinese research group that goes by Xfocus, Maiffret said.
Non-Microsoft systems were not vulnerable, though some may have had trouble connecting with Web sites, e-mail and other servers that run on Windows.
— The Associated Press and staff writer Scott Rothschild contributed information to this report.